Forbes Magazine published an article about Crown Sterling’s new entrant into the rapidly expanding Data Sovereignty Industry: ‘TIME AI’
Excerpt from the article: “Defying convention, Grant has arisen to take up the fight for data sovereignty in a surprising twist of fate. Not long ago, he was primarily known in the business world for his C-Suite accomplishments. The onetime CEO/President of Bausch and Lomb Surgical, he previously served as president of Allergan Medical, both billion-dollar organizations. What may have been less known is Grant’s polymathic tendencies. An accomplished sculptor, artist, and musician who can fluently speak eight languages, he holds patents and intellectual property in the fields of DNA and phenotypic expression, human cybernetic implantology, biophotonics, and electromagnetism.
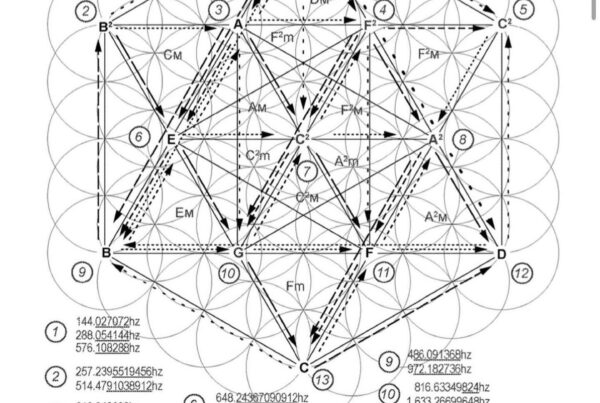
Then one day, he discovered new math that would transform encryption. “I found a new type of number that, using a particular geometry called an Icositetragon, a polygon with 24 sides (like a 24-hour clock), has characteristics that are prime-like, except are not prime,” says Grant. “And what makes them prime-like is that instead of being divisible by any kind of number, they’re divisible only by large prime numbers (expressly excluding small prime numbers two and three).” Grant’s findings have since been published by Cornell University in a paper co-authored by Physicist and Number Theorist Talal Ghannam PhD entitled, “Accurate and Infinite Prime Number Prediction from Novel Quasi-Prime Analytical Methodology.” This discovery matters because today’s encryptions are based upon numbers generated by multiplying two primes to obtain the public key encryption, a process called factorization. Essentially, the whole system we rely on for internet security today rests upon the time it takes a computer to back-calculate what A and B would be if you only knew C. Grant’s discovery allows us to predict prime numbers we could not before.
Grant is quick to confess he didn’t set out to disrupt encryption protocol by exposing factorization’s vulnerabilities. It was an unintended breakthrough.”
Read the full article here: https://www.forbes.com/sites/cognitiveworld/2019/07/21/its-time-to-fight-back-for-data-sovereignty